Core Technology = Tor (The Onion Router)
Key Feature = Multi-layer anonymization
Primary Use = Privacy + hidden services
What is the Tor Network?
Tor (The Onion Router) is the foundation of the dark web. It is a decentralized network that routes internet traffic through multiple nodes, encrypting data at each step to hide its origin and destination.
Instead of connecting directly to a website, your request travels through a chain of relays, making it extremely difficult to trace.
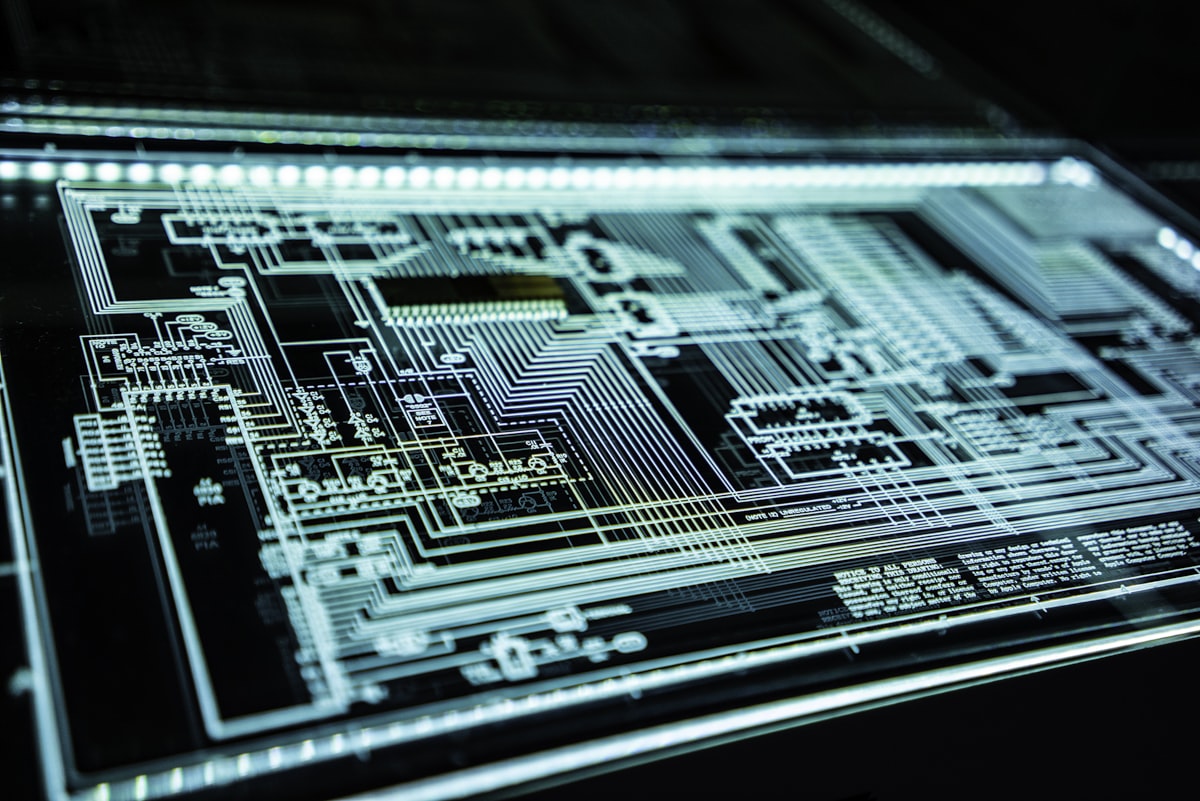
How Onion Routing Works
Onion routing is the core mechanism behind Tor. Data is wrapped in multiple layers of encryption—like layers of an onion.
Each relay in the network removes one encryption layer, revealing only the next destination, not the full path.
Each step = encrypted layer removed
No single node knows full route
This design ensures that no single point in the network can identify both the sender and the receiver.
What Are Hidden Services (.onion)?
Hidden services are websites that exist entirely داخل the Tor network. They use .onion domains and are not accessible through normal browsers.
Unlike traditional websites, both the user and the server remain anonymous.
This allows platforms to operate without revealing physical location or infrastructure.
Encryption Layers and Privacy
Tor uses layered encryption combined with randomized routing paths. Every connection is rebuilt dynamically, preventing consistent tracking.
This makes surveillance significantly harder compared to the surface web.
Why This Matters for Cyber Intelligence
Understanding how the dark web works is essential for threat intelligence.
Attackers rely on this infrastructure to:
• Trade stolen credentials
• Share exploits
• Coordinate attacks
• Sell unauthorized access
Organizations counter this by monitoring hidden services and analyzing traffic patterns across anonymized networks.
Strategic Insight
The dark web is not dangerous because of its technology. It is dangerous because of how that technology is used.
Tor enables privacy—but it also enables invisibility.
And in cybersecurity, what cannot be seen cannot be controlled.
For a full breakdown of the ecosystem, see Dark Web Secrets: Core Intelligence Overview.